Software patches are more than routine updates; they are ongoing maintenance that keeps systems secure, compliant, and performing well. In today’s fast-paced IT environment, attackers continually seek unpatched software to exploit, making timely patches a critical defense. This article demystifies patches, explains why updates matter, and offers a practical, repeatable approach to applying them across devices, servers, and cloud services. By embracing a structured patching mindset and using the right tools, organizations can reduce risk, minimize downtime, and strengthen defenses with security patches across endpoints and servers. The focus here is on Software patches and how they fit into a broader patch management strategy, including the importance of software updates and how to apply patches without disrupting daily operations.
In other words, the ongoing practice of software remediation involves timely fixes, security updates, and vulnerability remediations that shield systems from threats. Think of these measures as maintenance releases that patch known flaws, close exposure, and maintain compatibility with evolving platforms. Organizations implement a coordinated patch management program, an approach that blends discovery, testing, deployment, and verification to minimize disruption. By reframing patches as proactive security updates and trusted fixes, teams can communicate value to stakeholders and align with governance needs.
What are Software Patches and Why They Matter for Security and Reliability
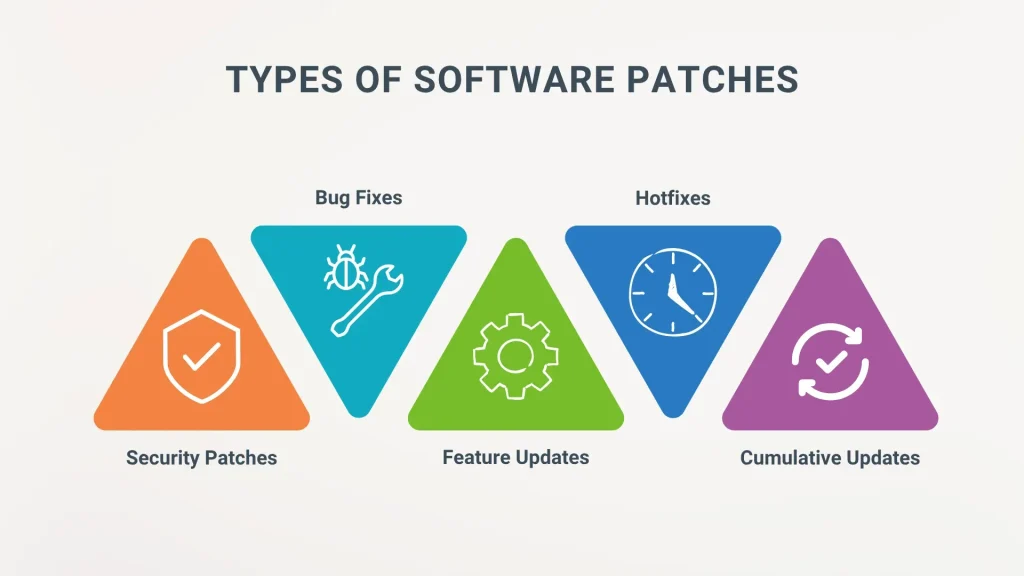
Software patches are code updates released by vendors to fix defects, close vulnerabilities, or add features. They address issues ranging from remote code execution vulnerabilities tracked in CVEs to performance enhancements, collectively reducing the attack surface and helping organizations stay ahead of exploits. In this sense, Software patches are a frontline defense that translates vendor fixes into actionable protections for your environment.
Adopting a disciplined patching mindset helps organizations reduce risk, improve reliability, and support compliance. Patches are not a one-time event but part of a broader patch management strategy that aligns asset inventories, vulnerability management, and change control with ongoing security hygiene and operational resilience.
Software Updates as the Foundation of a Secure Patch Management Strategy
Software updates are the regular releases that keep applications compatible with operating systems, libraries, and cloud services. When viewed through the lens of patch management, updates create a predictable cadence that minimizes security gaps, performance issues, and downtime. This cadence ensures that critical fixes reach production systems without causing unnecessary disruption.
A robust approach ties updates to governance, risk management, and compliance. By testing, staging, and communicating plans, organizations can apply security patches promptly while preserving service availability, thereby sustaining trust with users and regulators alike.
A Repeatable Patch Management Lifecycle: From Inventory to Verification
A repeatable patch management lifecycle begins with thorough inventory and discovery. Maintaining an up-to-date view of hardware, operating systems, applications, and cloud services—and coupling this with vulnerability scanning—highlights which software patches are most urgent and where they will have the greatest impact.
From risk assessment to verification, this lifecycle emphasizes testing, deployment planning, staged rollouts, and ongoing monitoring. By documenting results and auditing patch levels, teams can continuously improve how they patch across endpoints, servers, databases, containers, and cloud workloads.
How to Apply Patches Safely: Practical Steps to Minimize Downtime
Applying patches safely starts with establishing a baseline inventory and a controlled testing regime. Create a representative testing environment that mirrors production where possible, verify patch install success, and confirm that key workflows remain intact before broader rollout.
Plan deployment windows to minimize business impact, back up systems beforehand, and prepare rollback steps. Use phased deployments—starting with non-critical devices or test groups—and monitor outcomes to ensure that application performance and user experience remain stable.
Prioritizing Patches: Security Patches, Risk, and Compliance Considerations
Prioritization should weigh exploit risk, asset criticality, and exposure. Security patches—especially those fixing remote code execution on internet-facing systems—deserve fast-tracking, while other fixes follow a risk-based schedule aligned with business priorities and regulatory requirements.
Keep up with vulnerability disclosures, threat intelligence, and governance requirements to ensure patching aligns with broader risk management. A well-prioritized patch program reduces risk across endpoints, servers, databases, and cloud services while supporting compliance programs.
Automation and Tools: Accelerating Patch Management Across Environments
Automation accelerates patch management by standardizing discovery, prioritization, testing, deployment, and reporting. It reduces manual effort, enabling scalable patching across large and diverse environments while maintaining consistency.
Leverage tools such as WSUS, SCCM, and cloud-native patching solutions, and integrate with vulnerability management and SIEM for a holistic risk view. Governance and change-control processes remain essential to ensure that automated patching complies with policies and operational requirements.
Frequently Asked Questions
What are Software patches and why do they matter in patch management?
Software patches are updates released by vendors to fix defects, close vulnerabilities, improve compatibility, or add features. They help reduce exposure by closing attack surfaces and mitigating risk, making them a core component of patch management. Treat patches as ongoing maintenance to protect systems, data, and operations.
How do software updates relate to security patches within a patch management program?
Software updates are ongoing releases that keep applications current; security patches specifically address vulnerabilities exploited by attackers. In patch management, timely delivery of software updates and prioritization of security patches reduces exposure and helps maintain compliance, reliability, and performance.
What is the best way to apply patches across devices, servers, and cloud services, and how to apply patches safely?
To apply patches across devices, servers, and cloud services, start with an accurate inventory, create a representative test environment, and run phased deployments during maintenance windows. Verify backups, monitor results, and be ready to roll back if needed. Use centralized patch management tools (like WSUS, SCCM, or cloud-native solutions) to automate and govern the process.
Why is patch management a repeatable process and how does it reduce downtime when deploying security patches?
Patch management is a repeatable lifecycle: inventory, assess risk, test, plan deployment windows, deploy and monitor, verify, and review. This discipline reduces downtime by validating patches in advance, staging deployments, and maintaining audit trails. Prioritizing critical security patches helps mitigate exposure quickly.
What are key steps and best practices for testing and deploying security patches?
Key steps include testing patches in a production-like environment, running pilots with a small group, validating backups, and deploying in controlled waves. Avoid rushing patches and monitor for issues after deployment. Document outcomes for governance and continuously refine the process.
Which tools and automation support patch management and software patches while maintaining governance?
Automation supports patch management at scale by automating discovery, prioritization, testing, deployment, and reporting. Use tools that integrate with vulnerability management and SIEM to get a holistic risk view. Establish governance with change controls, approvals, and rollback plans to keep patches effective and compliant.
| Aspect | Key Points |
|---|---|
| What are Software patches? | A patch is code released by a vendor to fix defects, close security vulnerabilities, improve compatibility, or add features. Patches reduce exposure by removing or lessening the attack surface and help protect against exploits (including CVEs). They range from minor to critical and may address performance or bug fixes as well. |
| Why updates matter | Security updates stop known exploits and prevent attackers from compromising endpoints, servers, or services. Updates also fix bugs, improve compatibility with libraries and cloud services, and support compliance, performance, and business continuity. |
| Patch management: a repeatable process | A patching lifecycle is repeatable and controllable. Key steps include: 1) Inventory and discover; 2) Assess risk and priority; 3) Test and validate; 4) Plan deployment windows; 5) Deploy and monitor; 6) Verify and audit; 7) Review and improve. Use a risk-based approach and maintain governance. |
| How to apply Software patches effectively | – Establish baseline and inventory: know what you have and track software versions. – Use centralized patch management tools (e.g., WSUS, SCCM, cloud patching) to deploy at scale. – Test patches before broad deployment. – Schedule maintenance windows and communicate impact. – Backup and plan rollback before applying patches. – Patch in stages and automate where possible while maintaining governance. – Address all layers (servers, endpoints, databases, containers, cloud services). – Do not skip testing for critical systems; align patches with security priorities. |
| Best practices and common pitfalls | Common pitfalls include rushing patches without testing, patch fatigue from ad hoc updates, neglecting legacy systems, ignoring third-party dependencies, and insufficient testing in production-like environments. Adhere to a predictable cadence and comprehensive validation to avoid disruption. |
| A practical deployment example | A typical cycle: Week 1—inventory and vulnerability scans; Week 2—pilot patching on non-critical systems; Week 3—production rollout in waves (critical servers first); Week 4—verify, update inventory, and generate compliance reports. |
| Automation, tools, and governance | Automation enables consistent discovery, prioritization, testing, deployment, and reporting. Tools integrate with vulnerability management and SIEM for a holistic risk view. Governance defines downtime allowances, change control, escalation paths for zero-day threats, and requires oversight even when using automated processes. |
Summary
Conclusion: Software patches are essential components of a modern security program. A disciplined patch management approach reduces risk, minimizes downtime, and helps maintain compliance and reliability across the organization. By following a repeatable process, validating updates, and using automation responsibly within strong governance, teams can apply patches effectively without disrupting operations while staying aligned with evolving threats and technology changes.